Access Management
Define access roles for the end-users of your applications and APIs, and extend your authorization capabilities to implement dynamic access control.
Organizations looking to enhance their security posture can integrate their Identity Access Management platform to provide hardware-based multi-factor authentication to all their users. This will not only provide the highest level of protection against phishing, but it will also ensure strong authentication of every user on the path to a Zero Trust model.
Identity Access Management (IAM) solutions ensure that the right users have access to the applications and data they need. provides a strength-in-depth approach to authentication that is 100% phishing-resistant, builds trust, and dramatically cuts support costs.
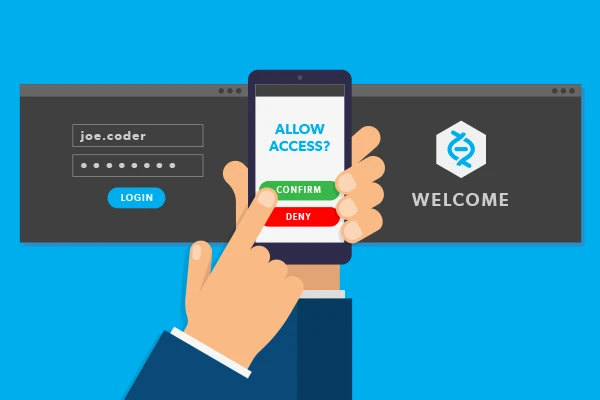
Multi Factor Authentication
Multi-Factor Authentication: is an authentication method that requires the user provide two or more verification factors to gain access to a resource such as an application, online account, or network environment.
Benefits: is used to increase the strength of identity and access management (IAM), it’s a core component for IAM.
- Network Access Control: NAC Technologies that enable organizations to implement policies controlling access to corporate infrastructure by both user-oriented devices and Internet of Things (IoT) devices. It’s an approach to computer security that attempt to unify endpoint security technology (such as anti-virus, intrusion prevention, and vulnerability assessment), user or security authentication and network security enforcement.
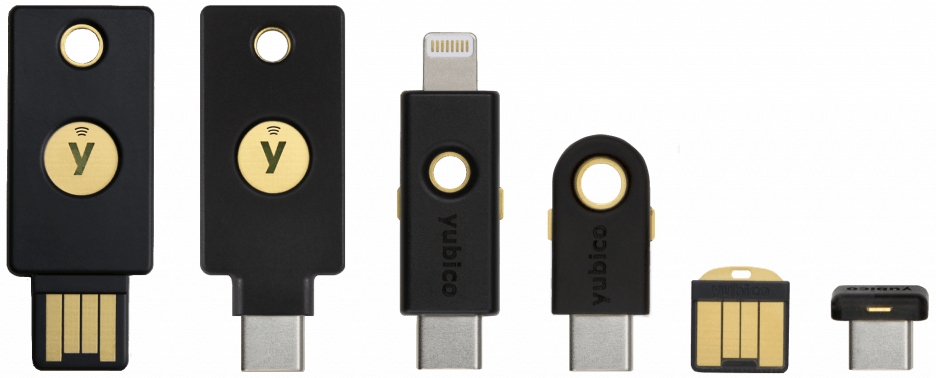
Token Authentication ( Yubikey )
YubiKey
Password-less future
The only technology proven to stop account takeovers at scale.
Used by 9 of the top 10 technology companies. Loved by more than 5,000 businesses and 15+ million users in over 160 countries.
Passwordless Authentication
Passwordless authentication is the process of verifying a software user’s identity with something other than a password. The most common passwordless authentication methods include verifying the possession of a secondary device or account a user has or a biometric trait that is unique to them, like their face or fingerprint.
Passwordless authentication can reduce costs and security risks for any organization. And as Google Cloud’s director of product management Sam Srinivas explains, passwordless authentication usage will likely grow rapidly in the near future.
Here is why more enterprises are turning to passwordless authentication and how you can implement it in your organization.

SoftToken Authuntication
Soft tokens are digital authentication keys. They’re called ‘soft tokens’ because soft tokens are based on software. Single-use authentication codes, authenticator apps, or clickable authentication links are all soft tokens.
Secure, Convenient Passcode Delivery
Soft token authentication is a simple and convenient method of verifying your identity and preventing fraud. Available to all eligible Business Online Banking customers, it helps prevent unauthorized access to your business accounts and keeps them safe and secure.
