Network security management helps reduce manual tasks and human errors by simplifying administration with security policy and workflow tools through a centralized management interface.
Network security management can reduce risk across the network and protect data by leveraging the information on threats, network vulnerabilities and their criticality, evaluating potential options to block an attack, and providing intelligence for decision support.
Policy administration is improved by unifying common policy tasks within a single interface, automating policy change workflow, including compliance audits and the management of multiple firewall vendors. This simplified and automated security policy management enables IT teams to save time, avoid manual errors, and reduce risk.

Thus, there are many solutions we can provide it and out of which are mentioned below.
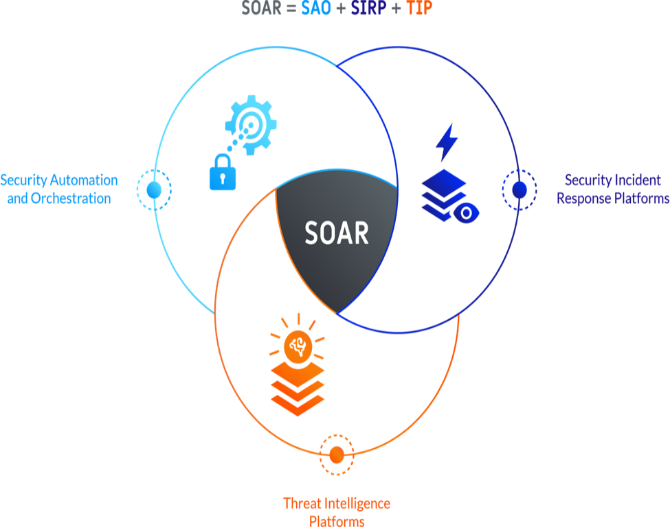
SOAR Security Orchestrate Automation and Response
Benefits: is used for threat and vulnerability management, security incident response, and security operations automation.
Note: Deploying SOAR and SIEM together in solutions makes the life of the SOC analysts easier
SIEM Security Information & Event Management
Benefits: is used to receives log data from many sources and can generate one report that addresses all of the relevant logged security events among these sources.

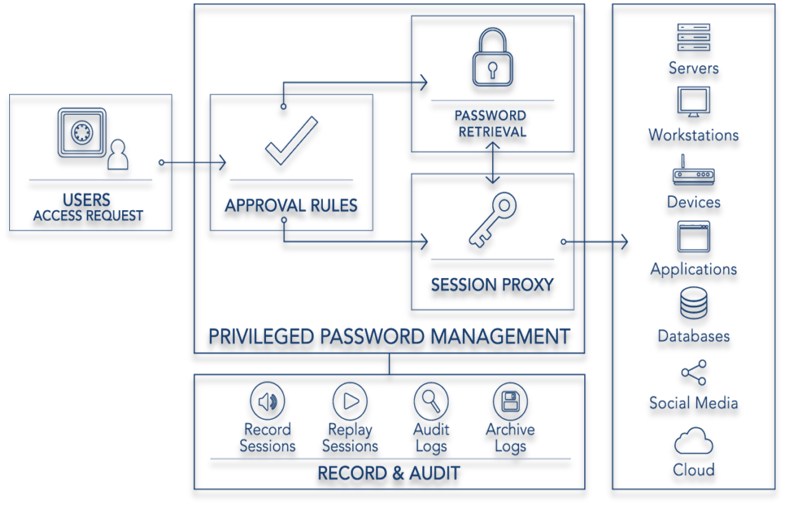
PAM Privilege Access Management
Benefits: is used to perform various types of tasks involving authentication, authorization and some modification (for example password change). It allows the system administrator to separate the details of authentication tasks from the applications themselves.
Data Loss Prevention – DLP
Data Loss Prevention: DLP is a strategy for making sure that end users do not send sensitive or critical information outside the corporate network. The term is also used to describe software products that help a network administrator control what data end users can transfer.is a set of tools and processes used to ensure that sensitive data is not lost, misused, or accessed by unauthorized users.
Benefits: used to ensure that sensitive data is not lost, missed, or accessed by unauthorized users.

Data Erasure & Destruction
Benefits: is used to reuse the storage device or make sure it cant be restore .

